Cloud-native CWPP, built on eBPF ensuring deepest possible security visibility with the lowest possible overhead. AI-powered runtime defense for servers, VMs, and containerized workloads in AWS, Azure, Google Cloud, and private cloud.
Automated. Agile. Secure.
Your Hybrid Cloud Footprint is Complex.
Cloud Workload Protection Shouldn’t Be.
Hybrid Cloud Workload Protection
Across AWS, Azure, GCP, and your private cloud or data center
- Real-time detection and response of runtime threats across servers, VMs, containers, and Kubernetes
- Stops threats such as ransomware, zero-day exploits, cryptominers, and fileless attacks
- eBPF agent architecture, for OS process-level visibility with no kernel dependencies, no kernel panics
- Support for 14 Linux distros, 20 years of Windows Servers, 3 container runtimes, Kubernetes
- Auto-discover unprotected cloud compute instances


AI-Powered Threat Detection & Response
Machine-Speed Defense vs Runtime Threats
- Multiple on-agent detection engines work seamlessly together
- Static AI Engine trained over half a billion malware samples, inspects file structure for malicious characteristics
- Behavioral AI Engine adds the dimension of time in assessing malicious intent
- Application Control Engine defeats rogue processes not associated with the workload image
- Threat Intelligence Engine identifies known-bad malware
- eBPF agent architecture achieves high security performance with incremental CPU and memory
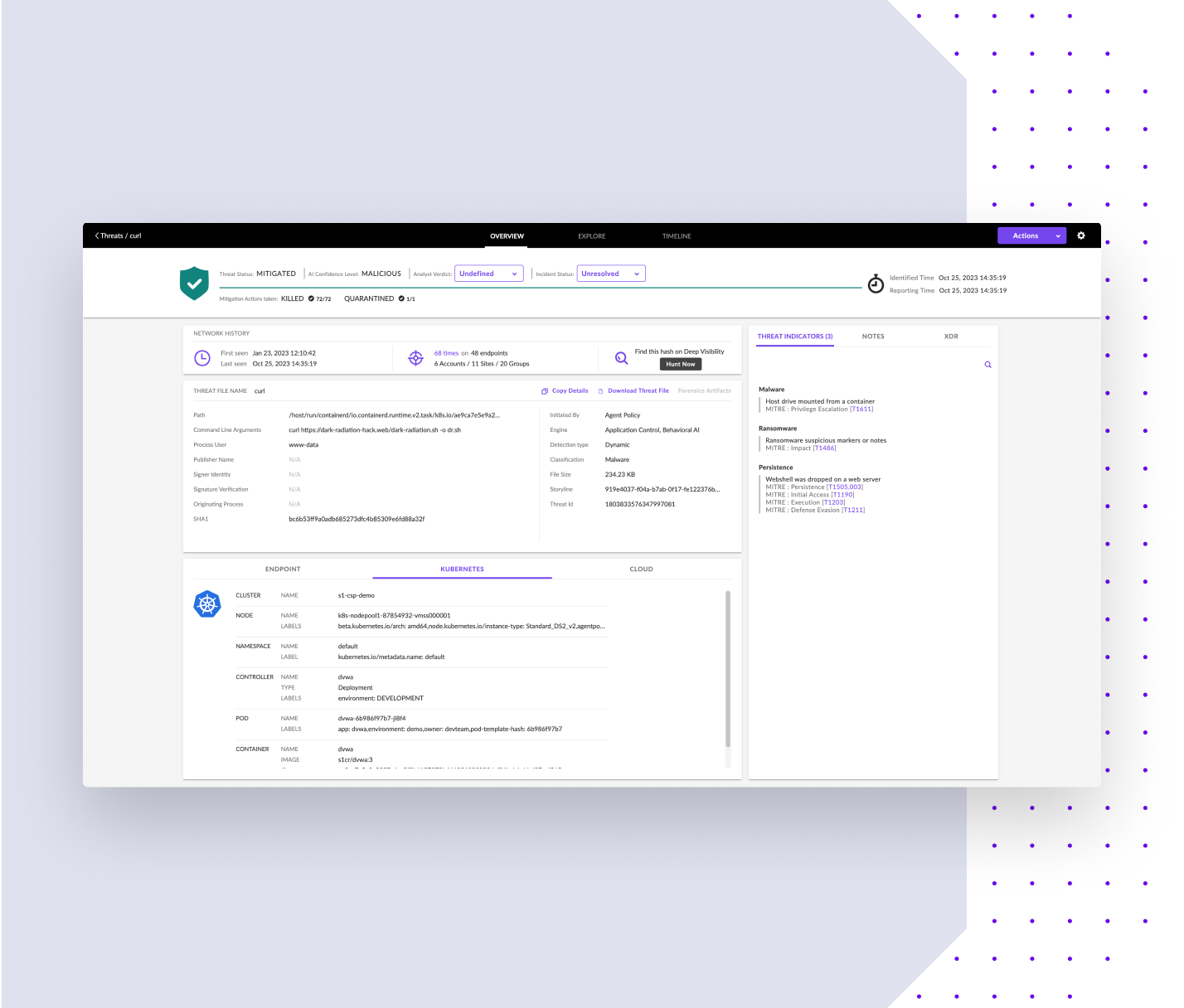
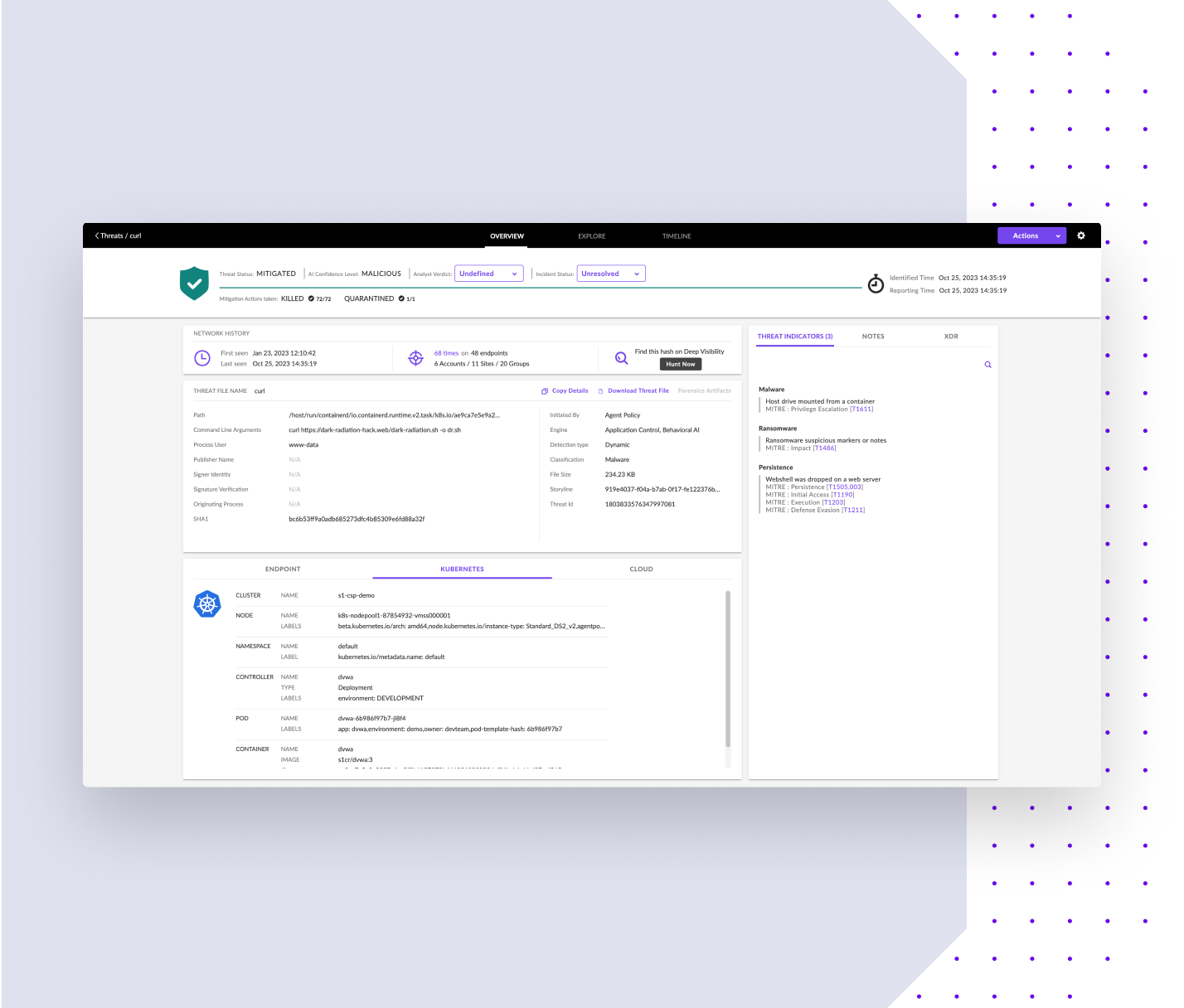
Comprehensive Forensic Visibility
OS process-level telemetry for incident response, triage, and threat hunting
- Petabyte-scale Singularity Data Lake for efficient search, intuitive threat hunting, and streamlined investigation across every file, process, and network event
- Automated Storyline™ attack visualization and mapping to MITRE ATT&CK TTPs
- Simplify forensic artifact collection at scale and execute customizable response workflows with RemoteOps
- Enrich runtime threat detections with build time context, cloud metadata, and more via Singularity Marketplace integrations


DevOps-Friendly
Automation, Scalability, Efficiency
- No Linux kernel dependency hassles
- IaC for DevOps provisioning
- Auto-scaling CWPP for self-managed and managed K8s (EKS, AKS, GKE)
- A single K8s CWPP agent per worker node protects the host OS, all its pods, all its containers
- Auto-deploy CWPP agent to cloud compute instances in AWS, Azure, Google Cloud
- Supports 14 Linux distros, 20 years of Windows Servers, and 3 container runtimes (Docker, containerd, cri-o)

